The Dark Web promises ultimate anonymity. By using the Tor Browser to hide their IP addresses and Bitcoin to hide their money, cybercriminals believe they are untouchable.
Yet, the biggest Dark Web kingpins in history-the founders of massive illegal marketplaces like Silk Road and AlphaBay-are currently sitting in federal prison or had their empires completely dismantled.
🛡️ Investigator Verified: NordVPN
Never conduct OSINT research or browse the Dark Web without encrypting your traffic. Your ISP logs your activity by default. We use and recommend NordVPN for its 100% RAM-only servers and strict zero-log jurisdiction.
30-Day Money-Back Guarantee
Did the FBI break the Tor encryption? Did they hack the blockchain? No. They caught them using Open Source Intelligence (OSINT). They looked for OPSEC (Operational Security) Failures.
No matter how good the encryption is, humans make mistakes. Here is how investigators exploit those mistakes to unmask the Dark Web’s most notorious phantoms.
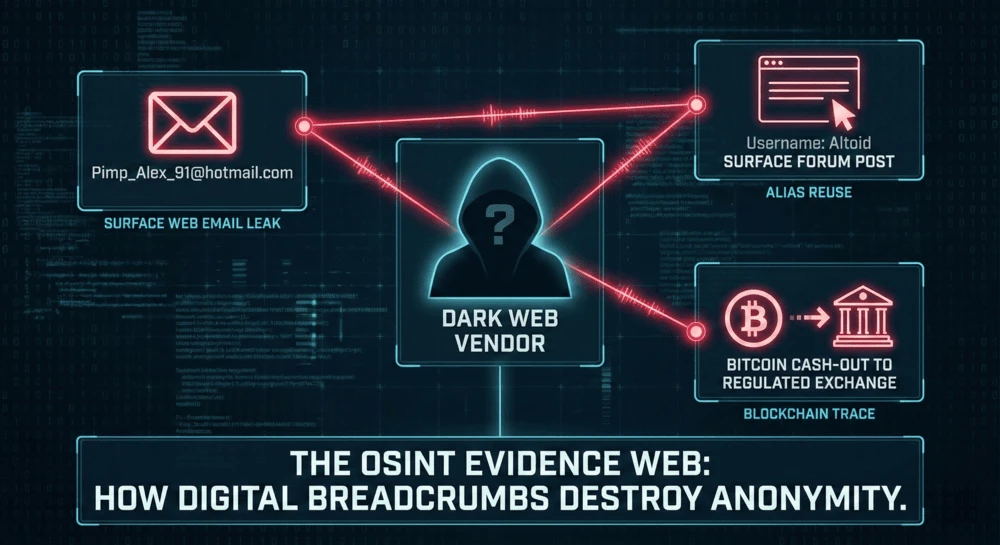
Method 1: The Email “Bleed” (The AlphaBay Takedown)
To stay hidden, a Dark Web vendor must maintain strict “compartmentalization.” Their illegal Dark Web persona must never interact with their real-world Surface Web identity.
If these two worlds touch for even a second, it is game over.
The Real-World Example: Alexandre Cazes ran AlphaBay, the largest Dark Web market in history. He was a millionaire criminal mastermind hiding behind the username Alpha02.
But in the early days of building his empire, he made a catastrophic mistake. When new users registered for AlphaBay, the server sent them an automated welcome email. In the raw header data of that email, investigators found the originating address: [email protected].
The OSINT Trace:
- Investigators searched the Surface Web for that Hotmail address.
- They found a 2008 post on a French tech support forum from a user named
Alpha02. - At the bottom of that forum post, the user had signed his real name: Alexandre Cazes.
His billion-dollar empire was brought down by an old Hotmail address he used when he was a teenager.
Method 2: Username Correlation (The Silk Road Error)
Lazy criminals reuse passwords. Arrogant criminals reuse usernames.
Before a newly created hidden site gets discovered and indexed by Dark Web search engines, the creator has to manually advertise it. They often go to Surface Web forums (like Reddit or crypto boards) to promote their hidden .onion link.
⚡ Exclusive OPSEC Discount
Military-grade encryption shouldn't break the bank. Avoid data-harvesting "free" apps and secure your digital footprint with a premium, audited no-log VPN. Lock in the lowest possible rate using our exclusive investigator link.
Special offer applies automatically.
The Real-World Example: Ross Ulbricht created the Silk Road, the first modern Dark Web market, under the fearsome pseudonym Dread Pirate Roberts.
However, before the site was big, he advertised it on a cryptocurrency forum using the burner username altoid. Months later, that same altoid account posted a job listing looking for an IT pro, asking applicants to send their resumes to [email protected].
The OSINT Trace:
- An IRS investigator found the old
altoidforum posts. - They connected
altoidto Ulbricht’s real Gmail account. - Furthermore, investigators found a post on the coding site StackOverflow asking how to code a specific Tor-hidden service. The user asked the question under his real name, “Ross Ulbricht,” before panicking and changing the username to “Frosty” less than a minute later.
The internet never forgets. That one-minute mistake gave investigators the physical target they needed.
Method 3: The Blockchain Bottleneck
The biggest myth in cybercrime is that Bitcoin is anonymous. It is not; it is pseudonymous.
Every single Bitcoin transaction in history is permanently recorded on a public ledger. While your real name isn’t on the ledger, your digital wallet address is.
The OSINT Trace: Investigators don’t care how many times a criminal bounces their Bitcoin around the Dark Web. They just wait.
Eventually, the criminal has to buy a real-world asset (like a Lamborghini or a house). To do that, they have to move their Bitcoin to a “Cash-Out” exchange (like Coinbase or Binance). Because these legitimate exchanges are heavily regulated, they require KYC (Know Your Customer) documentation, like a driver’s license or passport.
The moment the dirty Bitcoin hits a KYC exchange, the criminal’s real name is permanently linked to their Dark Web wallet.
Summary: The OPSEC Failure Matrix
| The Mistake | The OSINT Technique | How it Unmasks Them |
| Email Leakage | Reverse Email Lookups | Connects a Dark Web admin email to a Surface Web social media profile. |
| Alias Reuse | Username Searching | Finds old forum posts where the criminal used their real name. |
| Cashing Out | Blockchain Analysis | Traces public crypto ledgers to regulated exchanges requiring ID. |
The Bottom Line
Encryption algorithms don’t get tired, but humans do. A Dark Web criminal has to be perfect 100% of the time to stay hidden.
An OSINT investigator only needs the criminal to make one mistake, one time, to bring the whole house of cards crashing down.
Next Step: You don’t have to be a criminal to practice good OPSEC. Protect yourself from stalkers and identity thieves by making sure you aren’t reusing the same usernames across the internet. Use our Free Username Investigation Guide to see how much of your life is publicly connected.
Frequently Asked Questions (FAQs)
How do dark web criminals get caught?
Dark web criminals are usually caught through a combination of operational security (OPSEC) failures and Open Source Intelligence (OSINT). Law enforcement tracks them when they reuse surface web usernames, leak personal email addresses in server configurations, or transfer illicit cryptocurrency to regulated exchanges that require real-world ID.
Can police track activity on the dark web?
Yes. While the Tor network hides IP addresses, police can track dark web activity using advanced methods. These include blockchain analysis to trace financial transactions, Network Investigative Techniques (malware) to unmask user IPs, and traffic correlation attacks to match encrypted data packets to specific users.
Is Bitcoin untraceable on the dark web?
No, Bitcoin is pseudonymous, not anonymous. Every transaction is permanently recorded on a public blockchain. Investigators use specialized tracking software to follow stolen or illicit funds from dark web wallets directly to real-world cryptocurrency exchanges, where criminals are forced to reveal their true identities to cash out.
🔒 Don't Leave Your Network Exposed
You now have the intelligence to protect yourself, but knowledge without action is a vulnerability. Before you navigate away to start your research, ensure your connection is mathematically encrypted and hidden from third-party tracking.
Setup takes less than 2 minutes.