You keep getting harassing messages on Instagram from a blank profile. Or a scammer is texting your phone, pretending to be the IRS.
You cannot see their email headers (like we taught you in our Email Tracing Guide), and you cannot ask the police to “hack” them. But you can trick them into revealing their exact location.
Cybersecurity professionals use a technique called a Digital Tripwire (or tracking link). You send the anonymous person a link; when they click it, the link silently grabs their IP address, device model, and location, and sends it directly to you.
Here is how to create a legal tracking link to unmask anonymous trolls and scammers.
What is a Tracking Link?
Normally, when you click a link, your device has to tell the website’s server exactly where to send the webpage data. That means your device is handing over its IP address.
A tracking link intercepts this process. It records the clicker’s IP address and then immediately redirects them to a normal, harmless webpage (like a funny YouTube video or a news article) so they never know they were tracked.
Method 1: The “Grabify” Method (Best for Quick Checks)
Grabify is the most famous IP logger on the internet. It is free, fast, and easy to use.
How to set it up:
- Find a normal, interesting link that your harasser would want to click. (e.g., A news article, a meme, or a link to a fake “Document”). Copy that URL.
- Go to the official site: https://grabify.link.
- Paste the normal link into the box and click “Create URL.”
- Grabify will give you two things:
The New Tracking Link: This is what you send to the scammer.
The Tracking Code: Save this! This is your private password to view the results.
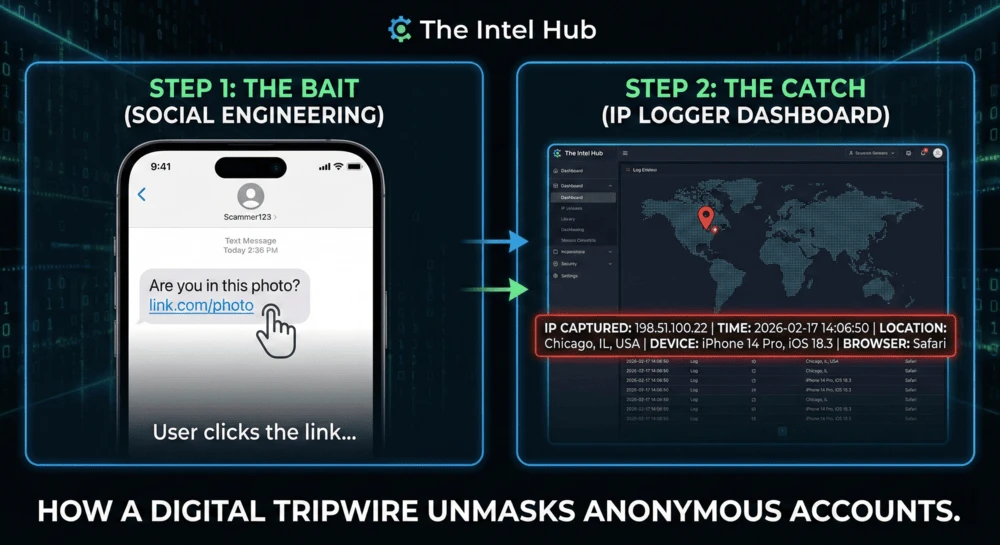
How to deploy it: Send the tracking link to the anonymous account. Use social engineering to make them click.
Example: “Is this picture of you? [Tracking Link]” or “I uploaded the receipt here: [Tracking Link].”
The Results: Once they click, go back to Grabify and enter your Tracking Code. It will reveal their IP address, their city, their internet provider, and exactly what kind of phone they are using.
Method 2: The “CanaryToken” Method (The Pro Choice)
Scammers are getting smarter. Many of them recognize a “Grabify” link and will refuse to click it.
If you are dealing with a sophisticated threat, you need to use CanaryTokens. This is a free tool built by professional cybersecurity researchers at Thinkst Canary.
Instead of just a web link, CanaryTokens allows you to embed a tracker into an actual Word Document or PDF.
How it works:
- Go to the official site: https://canarytokens.org.
- Select “MS Word Document” from the drop-down menu.
- Provide your email address (so the tool can alert you).
- The site generates a blank Word document. You can rename it something tempting, like
Financial_Records_2026.docx. - Send the document to the scammer.
The Trap: The moment the scammer opens the Word document on their computer, the document silently “calls home” and emails you their exact IP address and location. They never even have to click a web link.
Step 3: What to Do With the IP Address
Once the trap is sprung and you have their IP address, do not confront them.
- Geolocate It: Plug the IP address into a database like https://www.iplocation.net to find their physical city and country.
- The Server Check: Use our Shodan OSINT Guide to see if the IP address belongs to a VPN or a proxy server farm, which tells you they are trying to hide.
- Block and Ignore: If the IP address shows they live in your actual town, take screenshots of the Grabify logs and the harassing messages. You now have actionable evidence to give to local law enforcement or school administrators.
Summary: The Tripwire Protocol
| Tool | Best For | How it Works |
|---|---|---|
| Grabify | Trolls / Casual Scammers | Creates a clickable web link that grabs their IP and redirects them. |
| CanaryTokens | Sophisticated Scammers | Embeds a hidden tracker inside a Word or PDF document. |
The Bottom Line
You do not have to be a victim to anonymous harassment. By using digital tripwires like Grabify or CanaryTokens, you take the power back.
Remember: Never use these tools for illegal purposes or to harass others. Use them to protect yourself, unmask bad actors, and gather evidence.
Next Step: Did the IP address trace back to an aggressive company trying to collect a fake debt? Use our Corporate OSINT Guide to investigate their legal standing.